CAPTIVE PORTAL ON VERSA
- Celal
- May 2, 2021
- 2 min read
Updated: Jun 2, 2022
Everyone who works in this sector knows the captive portal. I won't explain to you what is the captive portal :)
Versa has a lot of features. This is amazing. Do these features work properly? One of the features is a captive portal. Let's see how to do this in Versa. Our topology is below.

I will make whole changes on branch device over Director.
First of all, I will create a certificate for SSL decryption. Why do we need a certificate? We need a certificate to be able to redirect HTTPS pages.
Captive Portal Setting;

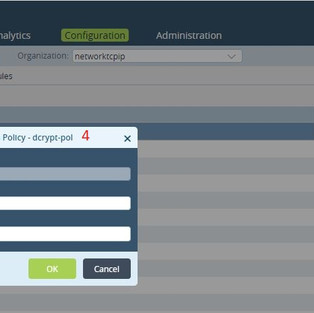
Decryption Setting;
The important part of this article is here. If we do not use decrypt policies. the portal page won't be redirected for HTTPS pages. Our versa device will be a man-in-the-middle device.
Also if we do not want it to decrypt all sessions after authentication, you can change the policy like below.
Authentication Setting;
I use a local database for authentication. As you wish you can use LDAP, Kerberos, and SAMP profiles.
Authentication Dns Rule;
Sometimes I had a problem with DNS resolution Therefore I write this rule on the top of the authentication policies.
Troubleshooting;
I have prepared a video to show you whether the captive portal is working properly.
if you watch the video, you won't see any SSL error. Because I have exported the SSL certificate which I have created before and installed my client. when you enter the HTTPS pages you will see the certificate which is issued by networktcpip.

Install the certificate on the Client;
As you wish, if you have a certificate authority. You can validate the certificate(CSR) on versa device from the certificate authority. Thereby you do not need to install the certificate manually to every client.
Thanks for Reading.






































Comments